Agentless Patch Management: Why We Chose Native Microsoft Integration
Frank writes about vulnerability management, patch operations, and Microsoft-native security workflows.
One of the most common questions we get from prospective clients is about our architecture: why agentless? In a market where most vulnerability management platforms require deploying agents to every endpoint, our decision to go native with Microsoft technologies is deliberate – and it comes from experience on both sides of the argument.
The real cost of agent deployment
Agents are software components that run on each managed endpoint. In theory, they provide granular visibility and control. In practice, they introduce a category of problem that has nothing to do with your actual security objectives.
I’ve rolled out endpoint agents across dozens of environments over the years – for system hardening, DLP, endpoint protection. The deployment phase is rarely the hard part. It’s what comes after.
One engagement stays with me. An organization of around 800 people deployed a DLP agent across their estate. Within days, blue screens started appearing on endpoints. What followed was two months of troubleshooting with the vendor – the most granular endpoint log analysis I’ve encountered, including ProcDump captures to isolate the conflict. The agent never fully stabilized. Eventually the organization cut their losses, dumped the tool entirely, and absorbed the cost of the whole exercise.
Another client ran an extensive Citrix environment that had grown faster than the underlying infrastructure could comfortably support. Any time there was a performance issue – and there were many – the Symantec DLP agent was the first thing that got disabled to rule it out as a cause. Fix the Citrix issue, then try re-enabling the agent. If something else surfaced, disable it again. Re-enabling it with enough confidence in its stability could take months. The net result was a DLP tool that was theoretically deployed but practically absent for significant stretches of time.
This is the pattern with agents in complex environments. The tool becomes the first suspect every time something goes wrong. The security team ends up spending its time troubleshooting the agent rather than focusing on the actual problem – vulnerabilities, exposure, remediation. The coverage gaps that result aren’t always visible, which makes them more dangerous, not less.
Why Microsoft-native changes the calculation
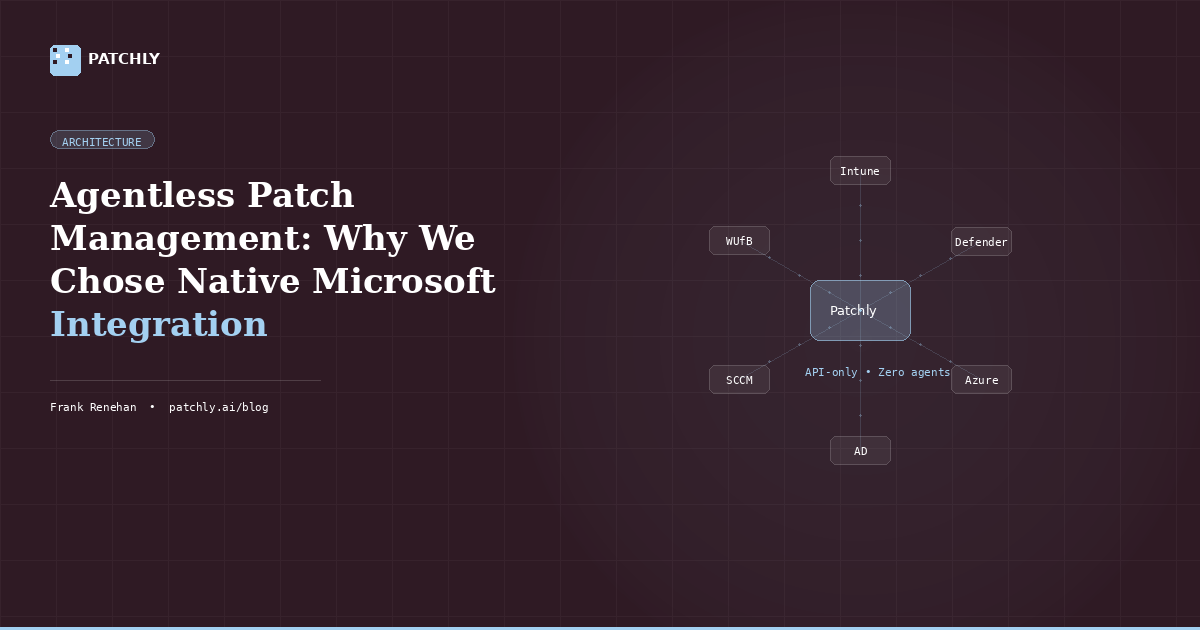
Patchly takes a fundamentally different approach. Instead of deploying our own agent, we leverage the management infrastructure that’s already running in your Microsoft environment.
Specifically, we use two capabilities that most enterprise Microsoft environments already have in place. Microsoft Intune gives us rich inventory data – device profiles, software installations, configuration state – without us needing to install anything. Microsoft Defender for Endpoint gives us vulnerability data, risk profiles, and broader security context across the asset estate. Together, they provide the telemetry and control plane we need to run a full vulnerability management program.
The deployment story changes dramatically as a result. There’s no rollout plan, no compatibility testing, no change management process for pushing software to 800 endpoints. If your devices are already managed by Intune and protected by Defender – and in most mid-market Microsoft environments, they are – Patchly can start delivering value within hours of onboarding.
The honest case for the trade-off
Agent-based platforms can offer deeper inspection for certain use cases, particularly in heterogeneous environments with a mix of operating systems, legacy hardware, and non-Microsoft software. We’re not the right fit for every environment.
What we are is a deliberate bet on a specific and well-supported architecture. The reason that bet makes sense comes down to a few things.
First, Microsoft environments are where most mid-market enterprise workloads actually run. Going deep on one robust vendor partnership – rather than trying to support the almost limitless combinations of devices, operating system versions, third-party agents, and application stacks – means we can build better integrations and maintain them more reliably. When Microsoft ships an OS update, we’re working with one integration to validate, not dozens.
Second, the Microsoft tooling is genuinely mature. Intune and Defender for Endpoint aren’t compromises – they’re enterprise-grade platforms with significant investment behind them. Using them as our data layer means our clients benefit from Microsoft’s ongoing development, not just ours.
Third, it eliminates a category of risk that agent-based approaches carry by default. Every additional piece of software running on every endpoint is a potential conflict, a potential failure mode, a potential liability in the event of an incident. Removing that variable is a meaningful security improvement in itself.
What this means in practice
For security and IT teams evaluating vulnerability management platforms, the agentless model changes the conversation in a few important ways.
Coverage is simpler. Every device that’s enrolled in Intune and running Defender is automatically in scope. There’s no deployment backlog, no exceptions list, no endpoints that missed the rollout.
Operational overhead is lower. There’s no agent to patch, no agent to troubleshoot, no support tickets when an update breaks something on a specific hardware model. The management plane is Microsoft’s problem, not yours.
And time to value is measured in hours rather than months – which matters when the alternative is spending two months troubleshooting blue screens before your security program has returned anything useful.
Related reading: Patch Tuesday Is a Starting Gun, Not a Finish Line | Your Attack Surface Is Bigger Than You Think
Evaluating agent vs. agentless for your environment? Book a demo and we’ll show you how Patchly integrates with your existing Microsoft infrastructure – no agents, no disruption.
In this article
Want to see how Patchly works? Request a free assessment or book a demo.